Your Trusted Partner in Cybersecurity Audit and Compliance Automation
Compliance Made Actionable With Quadshield
Quadshield helps you simplify cybersecurity compliance across every layer of your infrastructure
Automate Compliance
internal auditing aligned with ISO 27001, SOC 2, and NIST CSF
Identify Risk
CVSS scoring and MITRE ATT&CK mapping to identify and rank risks
Enforce Controls
Protects your endpoints and networks using Zero Trust
Be Audit-Ready
ensuring you pass ISO, SOC 2, or HIPAA audits without last-minute chaos
AuditReady
Your internal audit partner on the path to compliance
From ISO 27001 to SOC 2 readiness, AuditReady accelerates your compliance timelines, and generate actionable reports. With built-in CIS Control mappings and automated evidence collection, it creates an audit trail aligned with leading frameworks.
EndpointGuard
Your first line of defense — fortified and monitored
From remote devices to core networks, EndpointGuard safeguards your environment. With continuous monitoring, automated quarantine, and AI-driven threat correlation, ensures zero-day exploits, ransomware, and phishing attacks never reach your core infrastructure.
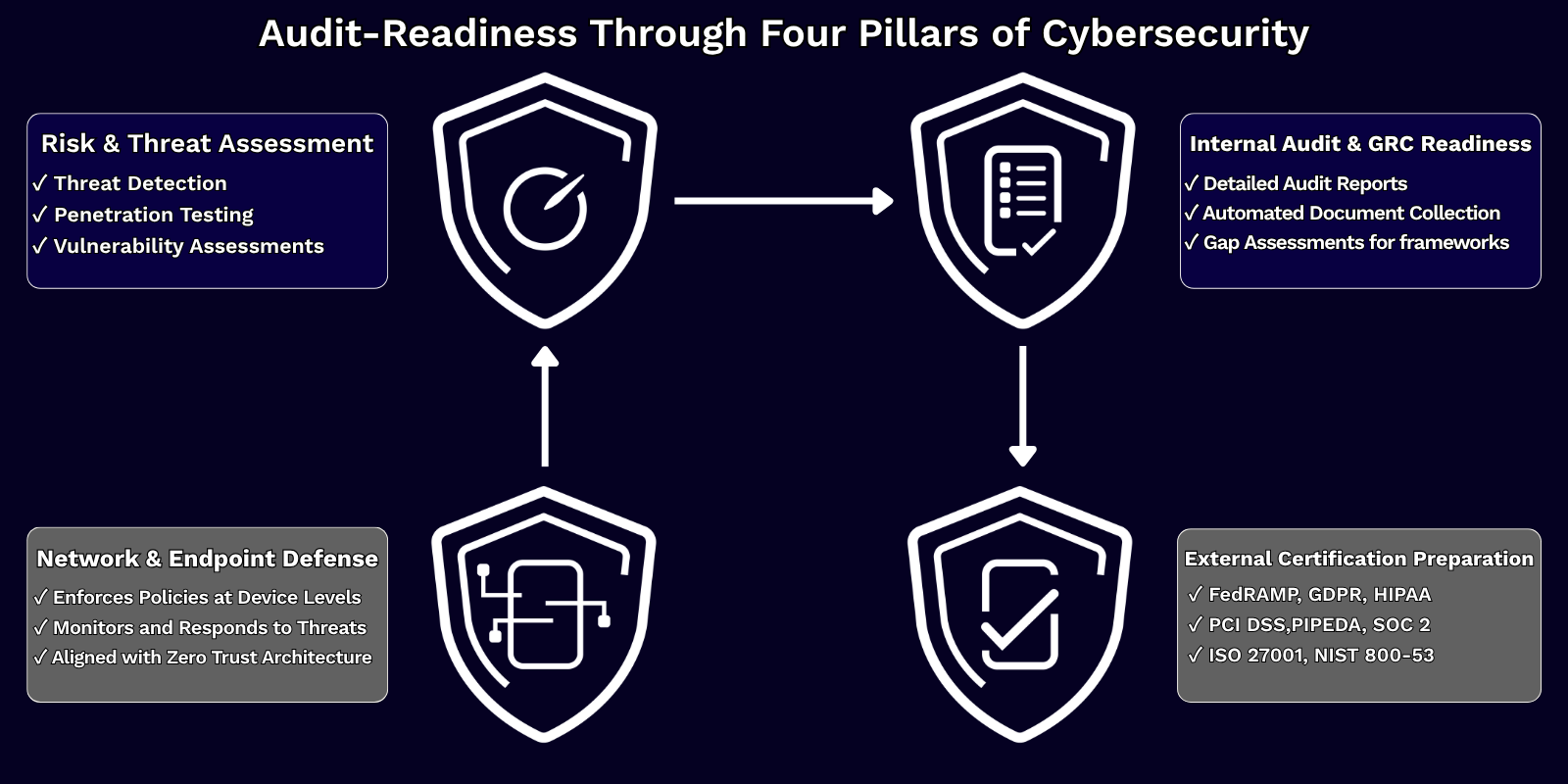
RiskSight
Know your risks before they become incidents
With penetration testing, and real-world vulnerability scans, it uncovers gaps across systems, processes, and third-party integrations. By turning threat intelligence into actionable business impact, ThreatLens lays the foundation for smarter security investments and audit preparedness.
CertFlow
Navigate compliance with confidence
Preparing for ISO 27001, SOC 2, HIPAA, and GDPR audits with precision. CertFlow offers clause-by-clause readiness tracking, policy alignment, and documentation curation and ensures that nothing is missed and every required control is mapped, reviewed, and validated.

AuditReady
Your internal audit partner
From ISO 27001 to SOC 2 readiness, AuditReady helps reduce manual effort, accelerate your compliance timelines, and generate actionable reports that satisfy both internal leadership and external regulators.
RiskSight
Identify risks before they become incidents
gives you deep visibility into your threat landscape, using tailored scans and assessments to identify weaknesses and potential attack paths.


EndpointGuard
Your first line of defense
Protect your organization’s most vulnerable assets — your devices and networks.
Ensure 24/7 threat detection, response, and resilience against evolving cyberattacks.
CertFlow
Navigate compliance with confidence
prepares your organization for successful certification by providing tailored assessments, milestone tracking, and detailed documentation support.

Frequently Asked Questions
Quadshield focuses on internal cybersecurity auditing and compliance automation. Our core services include risk and threat assessments, internal audit readiness, external certification preparation, and endpoint security.
Organizations of any size preparing for compliance frameworks like ISO 27001, SOC 2, HIPAA, or GDPR can benefit from our services. We support startups, SMBs, and enterprises looking to strengthen their cybersecurity posture.
Our AuditReady platform automates documentation, maps controls to standards, identifies gaps, and generates audit-ready reports. We make your team’s audit preparation process smooth and efficient.
Unlike generalist cybersecurity firms, Quadshield is purpose-built for compliance and internal auditing. We integrate risk intelligence with automation, offering technical depth and compliance expertise without the overhead.
No. Many of our clients use our services for internal security improvements, gap analysis, or to meet regulatory requirements without undergoing full certification.
While Quadshield primarily focuses on compliance and auditing, we partner with industry-certified pen testing providers. Our risk assessments often recommend and coordinate pentests as part of your roadmap.
Absolutely. Quadshield offers pre-audit assessments, evidence collection, and milestone tracking to ensure you pass certifications like ISO 27001, SOC 2, PCI-DSS, and others confidently.
Our RiskSight goes beyond automated scans. It includes risk scoring, attack vector mapping, and business impact analysis aligned with frameworks like NIST CSF and CIS Controls.
Yes. Our platform and services are tool-agnostic and can integrate with SIEM, vulnerability scanners, and compliance trackers like Jira, Microsoft 365, or AWS Security Hub.
You can start by completing the “Let’s Talk” form below. Our team will contact you as soon as possible to assess your needs and recommend a service package aligned with your compliance goals and risk environment.